Browser Agents in Production: What Actually Works in 2026
Setting up a browser agent takes five minutes. Getting reliable data from protected sites takes weeks. Here's what I learned running Camoufox, Agent TARS, and residential proxies against Cloudflare, DataDome, and Akamai.
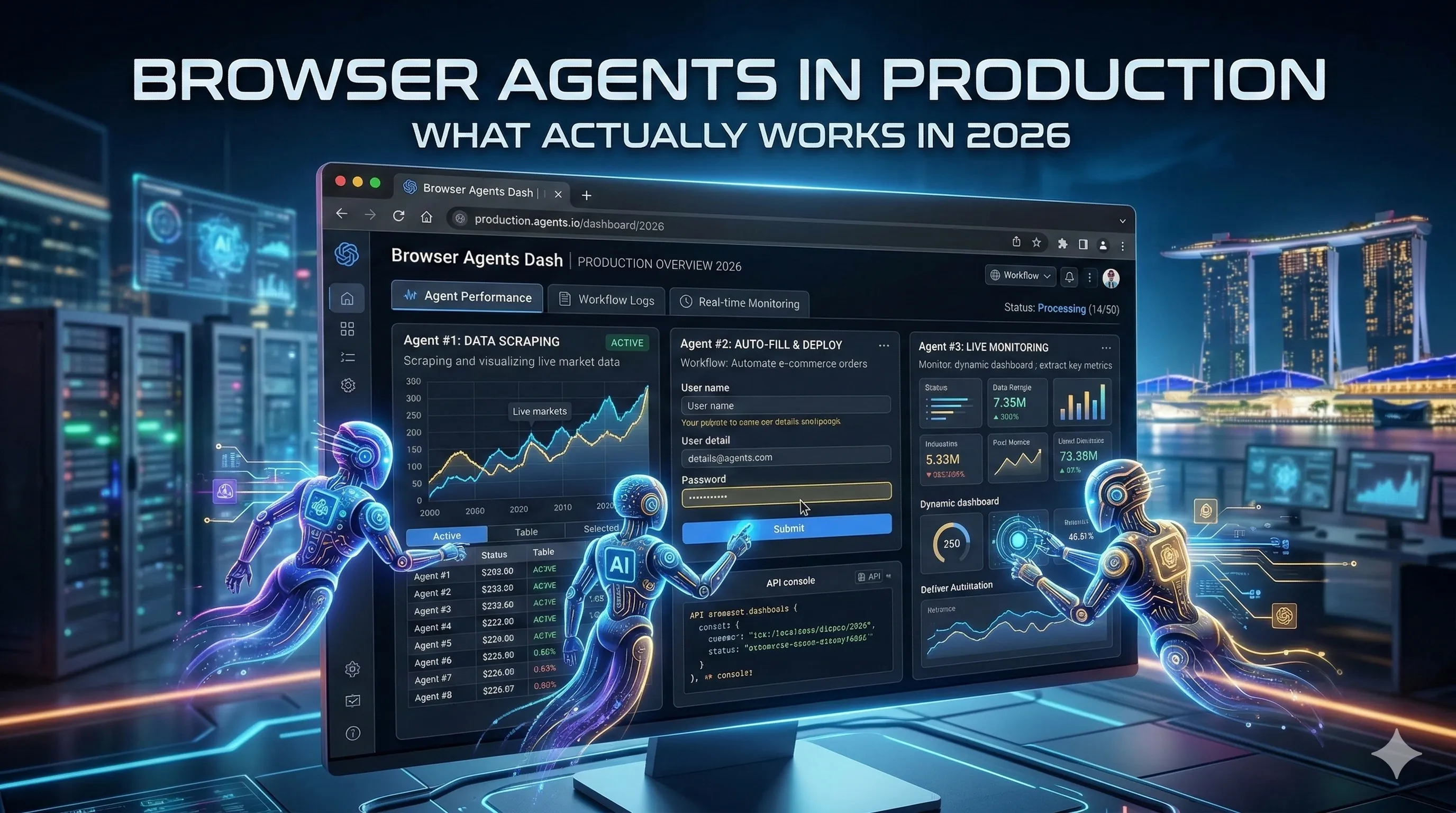
Setting up a browser agent takes five minutes. Getting reliable data from Amazon or Airbnb takes weeks of debugging anti-bot systems, proxy rotation, and fingerprint evasion. The gap between demo and production is where most automation projects die.
The AI browser market hit $4.5 billion in 2024, growing at 32.8% CAGR toward a projected $76.8 billion by 2034 (Market.us). GitHub confirms the demand: Firecrawl at 88K+ stars, Browser Use at 79K+, Stagehand at 21K+. Developers are building browser automation tools because the existing ones keep losing to anti-bot systems.
Standard Frameworks: When Playwright Is Enough
For simple jobs, standard tools work. Scraping unprotected pages, running test suites, automating internal dashboards. Don't overcomplicate these.
Playwright leads with 45.1% adoption among QA professionals (TestGuild 2025 survey). Deserved: stable API, solid docs, all major browsers. Microsoft invested seriously, and it shows.
Browser Use (79K+ GitHub stars) and Stagehand (21K+) add AI capabilities on top of Playwright. They interpret natural language tasks and generate browser actions automatically. For prototyping and unprotected targets, they save hours of writing selectors by hand.
The wall: all these tools run standard Chrome or Firefox. Cloudflare, DataDome, Akamai detect them within seconds. If the target has any serious protection, standard automation folds on the first request.
The Anti-Bot Arms Race: Why 2024 Playbooks Stopped Working
This is the part most "browser agent" tutorials skip.
In March 2025, Cloudflare deployed AI Labyrinth. It generates entire networks of fake pages filled with AI-written scientific content, linked from invisible honeypots on protected sites. A bot follows a link, lands on a convincing page about quantum physics, follows another link, gets deeper into the maze. Four clicks in, Cloudflare has its fingerprint. As their team put it: "No real human would go four links deep into a maze of AI-generated nonsense." The bot wastes compute on worthless data. The site learns exactly what automated traffic looks like.
This is the new baseline. Anti-bot systems don't just block anymore. They deceive, fingerprint, and learn.
And Cloudflare is one layer of four.
Per-site ML models analyze mouse trajectories, scroll velocity, and click timing. Humans are sloppy and inconsistent. Bots are precise. That precision is the tell.
Canvas and WebGL fingerprinting catch rendering differences between real and headless browsers. One pixel drawn wrong flags the session.
TLS fingerprinting (JA3/JA4) reads the handshake signature before the page even loads. Automation libraries produce different hashes than real browsers. The page hasn't rendered yet and the server already knows.
To pass all four layers: a stealth browser, residential proxies, and human-like behavior. Drop any one and detection climbs fast.
Stealth Browsers: The Actual Solution
Standard browsers leave fingerprints at every layer. Canvas rendering, WebGL output, TLS signatures. Even with JavaScript disabled, sites collect enough signal through CSS and HTML structure alone.
Camoufox is a Firefox fork rebuilt for anti-detection. In my testing, it passes 21 of 23 checks on sannysoft.com. The remaining two are proxy-related and fixable. Active community, solid documentation at camoufox.com.
Nodriver takes the Chrome-based approach. Less mature, developing fast. Both support proxy rotation, which is non-negotiable for production. One blocked IP rotates to the next mid-session.
I tried the obvious path first: Playwright with stealth plugins, custom headers, randomized delays. It worked for about a week. Then Cloudflare updated their detection and everything broke overnight. Camoufox with residential proxies survived the same update without a single change. The difference is architectural. Plugins patch over a detectable browser. Camoufox is built to be undetectable from the ground up.
My Stack and What It Costs
I run Camoufox for browsing, Agent TARS (Kimi K2.5 via OpenRouter) for AI-driven control, and IPRoyal residential proxies for IP rotation. The VPS is a $6 Contabo instance. Total: $55-110 per month depending on LLM volume.
| Component | Monthly Cost |
|---|---|
| Camoufox | Free (open source) |
| Agent TARS | Free (self-hosted) |
| LLM (Kimi K2.5 via OpenRouter) | $20-50 |
| Residential proxies (IPRoyal) | $30-50 |
| VPS (Contabo) | $5-10 |
| Total | $55-110 |
For comparison: ScrapingBee starts at $25 per GB, Bright Data at $500 per month, Apify at €49 for 100 actor units without anti-bot guarantees. Self-hosting costs less and gives full control. The trade-off is your time for setup and debugging. The "free" tool that can't collect data costs more than the paid one that can.
The debugging is real. Specific gotchas I burned hours on:
- GitHub OAuth: the "Continue with Google" button intercepts form submission. No amount of clicking works in headless. The workaround was bypassing the UI entirely through direct API calls.
- Proton Mail TOTP: six separate
input[inputmode='numeric']fields instead of one. Standard fill writes to the first field and stops. Each field needs individual targeting and input. - React dropdowns: they don't populate in headless mode with standard fill methods. The fix is click, then wait for a specific DOM mutation event.
sleep(500)works until it doesn't. Event-based waits work always.
Each of these took hours to discover and minutes to fix. The knowledge compounds. After a month of running this stack daily, the failure modes are mapped and the system runs unattended.
Decision Framework
Match the tool to the resistance:
Open pages, no protection. Playwright. Free, fast, reliable. Don't add complexity you don't need.
Moderate protection. Browser Use or Stagehand with rotating proxies. The AI layer handles DOM changes gracefully. Proxies cover basic IP detection.
Serious anti-bot (Cloudflare, DataDome, Akamai). Camoufox plus residential proxies. Add Agent TARS if you need AI-driven navigation. This is the stack that survives anti-bot updates without code changes.
The Race Doesn't Stop
A year ago, rotating User-Agents and adding random delays was enough for most sites. Today that approach fails on any site worth scraping. A year from now, AI Labyrinth will look primitive compared to whatever comes next.
The tools that win are the ones built to be indistinguishable from real browsers at every layer, not the ones that patch over detectable foundations. Pick your tools with that trajectory in mind.